Beyond the Perimeter: A Zero Trust Blueprint for Data Resilience
Backup systems are the last line of defense when ransomware, insider misuse, or natural disasters strike. Historically, these environments operated under the assumption that internal users were trustworthy—a model that is now obsolete.
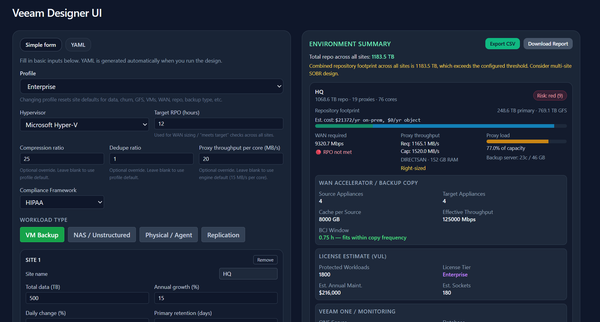
In my latest whitepaper, "Zero Trust Architecture for Enterprise Backup Infrastructure," I outline a standard-aligned blueprint for reimagining data protection based on NIST SP 800-207 and the CISA Zero Trust Maturity Model.
Key Architectural Pillars:
- Assume Breach: Design under the assumption that attackers may already have a foothold in your network.
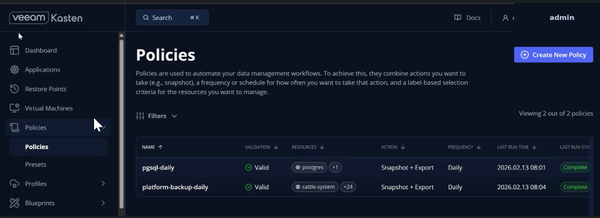
- Continuous Verification: Authenticate and authorize every request—including management consoles, repositories, and agents—regardless of their location.
- Least Privilege: Use just-in-time access and "four-eyes" approval workflows for destructive operations like deleting repositories.
- Micro-segmentation: Isolate the backup management plane so it is unreachable from general user workstations.
- Immutability: Use object-lock or WORM media to ensure retention policies cannot be overridden by a single administrator.
By applying these principles, organizations can transform backups from a soft target into a resilient, monitored, and trustworthy resource.
Download the Full Whitepaper:https://github.com/eblackrps/docs